There are no search terms available.
Monthly Archives: May 2021
-
Read more »
According to IDC, organizations worldwide collectively generated more than 64.2 zettabytes of data in 2020
-
Read more »
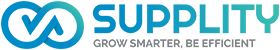
Zoned Storage is an open, standards-based initiative to enable data centres to scale efficiently for the zettabyte storage capacity era.
-
Posted: May 23, 2021Categories: ArticlesRead more »
VIVOTEK Smart VCA is the next-generation video analytics suite running on VIVOTEK cameras for security applications. The on-board Smart VCA suite includes Intrusion Detection, Loitering Detection, Line Crossing Detection, Unattended Object Detection, Missing Object Detection, Face Detection, Crowd Detection, and Running Detection
.
-
Read more »
The path to building a successful business is rarely a simple one.
But in the beginning, it seems simple enough: you’ll build an amazing product, market it and watch as people pull out their credit cards. Then you’ll hire people to take over menial tasks and you’ll move into the role of CEO, eventually delegating that as well and living on the beach in Bora Bora, sipping on a martini.
<
-
Posted: May 15, 2021Categories: Learn with SUPPLITYRead more »
Firewalls are a key aspect of network security. Firewall solutions are implemented to dictate incoming and outgoing network traffic using a mix of security rules created by the network administration team. By setting restrictions like access authorization and allowed/blocked websites, businesses create a barrier between their own protected network and untrusted external servers and sites
-
Posted: May 14, 2021Read more »
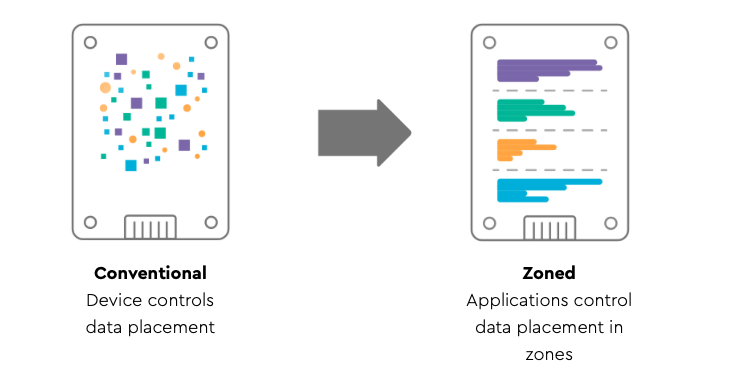
There are four types of wireless networks -- wireless local area networks, wireless metropolitan area networks, wireless personal area networks, and wireless wide area networks -- each with its own function.
Below we discuss the different types of wireless networks and the various equipment and connections they require
.
-
Posted: May 10, 2021Categories: ArticlesRead more »
Did you know that only one percent of cold calls even lead to an appointment, according to a popularly cited study by Baylor University's Keller Center for Research? The problem with cold calling is that it lacks a personal touch. Most of the time, the sales rep doesn’t offer anything the customer wants, because they don’t know what they want.
-
Posted: May 08, 2021Categories: News & EventsRead more »
-
-
Dell Technologies (NYSE:DELL) is unveiling solutions and partnerships designed to extract more value from data at the edge. The new offerings are part of the company’s edge strategy to deliver fully integrated technologies that allow workloads to run and be managed across multiple clouds and applications.
Cisco CEO Chuck Robbins
<!
-
-
-
Read more »
Organizations are increasingly on a path to evolve their edge-to-hybrid cloud IT estate. Driving this trend are new business models and the effort to capture the agility, operational efficiency, and innovation presented by digital transformation.
IDC estimates the economic value of digital transformation will represent almost $19 trillion
-
Posted: May 04, 2021Categories: News & EventsRead more »
HPE today announced innovations that transform HPE Storage into a cloud-native, software-defined data services business. As part of today’s news, HPE unveiled a data services platform that delivers on its Unified DataOps vision for a new data experience that brings a cloud operations model to wherever data lives and unifies data operations.
<!
- Learn with SUPPLITY (3)
-
Articles
(35)
- Cyber Security (3)
- Tech Infrastructure (1)
- Internet of things (2)
- Cloud Solutions (1)
- Bigdata (1)
- HPE Greenlake (1)
- Digital Transformation (1)
- News & Events (11)
- GLOSSARY (0)